The recent cybersecurity incident disclosed by Stryker on March 11, 2026, which caused global disruption to an aspect of their Microsoft environment. In their disclosure, Striker said it activated their cyber‑response plan, engaged outside advisors and cybersecurity experts, and believed that the incident was contained.
An Iran‑linked hacking “persona group” known as Handala claimed responsibility for the attack. According to news sources Reuters, the Handala group’s logo appeared on login screens, and Reuters cited outside accounts describing remote Windows devices – including phones and laptops managed by Intune as being wiped.
Stryker published a customer update (to customers) stating that the disruption appeared contained to its internal Microsoft environment, and that their other products including Mako, Vocera, and LIFEPAK35 remained safe to use.
At time of writing, Microsoft has not issued a public incident-specific statement about Stryker. There is no Microsoft confirmation that Intune was used to wipe devices in this case, nor any validation of the attacker’s claims. That distinction is important and aligns with how Microsoft typically communicates during customer incidents.
This is a stark reminder of something every organisation needs to internalise:
What Happened and why it matters
The Stryker incident is important not only because of the suspected attribution, but because it highlights a broader reality for every organisation that lives or exists in the cloud.
Any cloud‑based management platform must be treated as part of your operational backbone. If it fails or is compromised, your business fails.
This is not about a single vendor or technology is about identity and access. The attack entry point could be:
- Microsoft Intune
- Cisco Meraki Dashboard
- Webex Control Hub
- Azure Management Portal
- Microsoft 365 Admin Center
- Salesforce
- NetSuite
- Dynamics 365
- Google Admin Console
- ServiceNow
You get the point! If your business is powered by cloud‑based services, that cloud service control planes need to be protected. As a business, IT need to manage identity, devices, access, policy, and data.
If an attacker gains meaningful control (by logging on successfully) over any of these, they won’t need ransomware. They can:
- Lock out administrators
- Push destructive configuration changes
- Disable MFA or Conditional Access
- Modify network or security policies
- Interrupt authentication
- Disrupt sales, finance, HR, or operational systems
- Stall your business without encrypting a single endpoint
This is the new reality:
Your Cloud Management plane is the new crown jewel.
Why This Matters
Identity is control pane and needs to be protected
Whether you’re logging into Intune, Meraki, Salesforce, or Azure, identity is the front door. If attackers compromise identity, they compromise everything behind it. IT need to ensure access to these portals is secured and protected with Zero Trust Principals.
Cloud management platforms are inherently high‑impact
Accessed from anywhere, these portals allow organisations to manage their entire estate – they can push changes to thousands of devices, users, or workloads instantly. That’s good for IT but create a real honey pot for attackers.
Privilege is the new blast radius
A single over‑privileged admin account (that is not protected) can be the difference between a contained incident and a global outage.
Operational continuity now depends on SaaS
If your CRM, ERP, or other admin portal is unavailable or compromised your entire business or business function can stop.
Protecting Cloud Control Planes
1. Treat every Cloud Management platform as Critical Infra
This applies to anything with a Cloud Front end – Intune, Meraki, Salesforce, Azure, Webex Control Hub – all of them.
- Enforce Risk-Based MFA (preferably phishing‑resistant)
- Use just‑in‑time access where available
- Remove standing Global Admin / Super Admin roles
- Require admin access to only be from a secure device or Cloud PC [Windows 365]
- Maintain break‑glass accounts stored offline
If it configures your business, it is critical infrastructure.
2. Audit every privileged role – and shrink them
Across all platforms:
- Who can change identity policy?
- Who can push device actions?
- Who can modify network or security settings?
- Who can create or modify applications or integrations?
- Who can access financial or customer data?
- Who can access and where from?
Most organisations discover the same thing: Too many people have too much access for too long.
3. Monitor every access and change in the control plane
Every major SaaS platform will provides:
- Audit and Access logs
- Failed logons attempts and lockouts
- Change logs
- Admin activity logs
- API logs
- Integration logs
Review them. Centralise them. Alert on them. Retain them longer than the default.
Microsoft, for example, defaults Entra audit logs to 30 days unless exported. Many organisations don’t realise this until it’s too late. These can be extended.
4. Protect non‑human identities
This is universal across Azure, Salesforce, NetSuite, ServiceNow, Microsoft 365.
Service principals, AI Agents, API keys, automation accounts, and integrations:
- Often have high privilege
- Cannot perform MFA
- Are long‑lived
- Are rarely reviewed
- Are frequently forgotten
- Have access to lots of things 24/7
Replace them with managed identities where possible. Rotate secrets. Remove unnecessary privileges. Audit them regularly.
5. Rehearse partial control‑plane failure
Rehearse business impact just like your network or WAN going down. If Intune, Meraki, Salesforce, or your CRM is unavailable:
- How do you communicate?
- How do you rebuild devices?
- How do you take and process orders?
- How do you support users?
- How do you rotate credentials?
- How do you recover access?
If you haven’t tested it, you don’t have a plan.
Deep Dive: Microsoft Intune
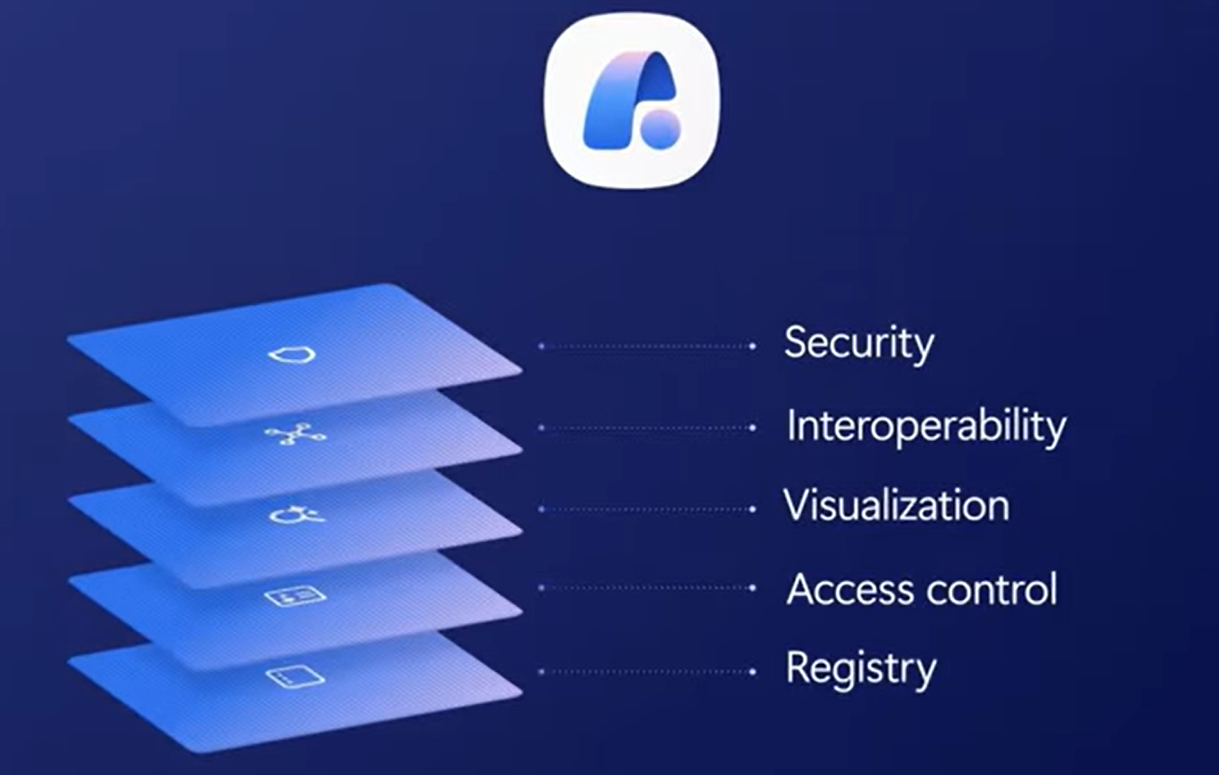
Since the Stryker attack was centered around Intune, I wanted to talk a little about this. is often the most powerful – and most misunderstood control plane in the Microsoft ecosystem. It can:
- Wipe devices
- Retire devices
- Push configuration
- Enforce compliance
- Control access
- Integrate with Defender for Endpoint
- Influence Conditional Access decisions
Here’s what organisations need to look at:
1. Review Intune roles and remove unnecessary privilege
Start with:
- A list of all Intune role assignments
- A list of all Global Administrators
- A list of all Privileged Role Administrators
- A list of all accounts with remote device action permissions
Review and Trim – If someone doesn’t need access (or needs occasionally) remove it!
2. Validate Conditional Access policies that depend on Intune
Look at and tighten:
- Which access policies require compliant devices
- Which policies enforce or require access from secure admin workstations
- Which policies protect / restrict access to admin portals
- Which policies protect high‑impact apps
This is where many organisations discover gaps.
3. Confirm Intune audit logs are exported
Ensure there is a process for:
- Exporting Intune logs to your SEIM or Log Analytics tool
- Exporting and reviewing Entra audit logs (via your SEIM or Log Tool)
- Making sure the right logs are kept for the right duration
- Triggering alerts for high‑impact actions – who needs to be woken up and when!
Do not rely on defaults. Review, Tweak and Change to meet your needs.
4. Require PIM for all privileged roles
This is a big one that many fail to do:
- Minimise and Restrict Global Admin Access
- Protect all Intune Administrator accounts
- Protect all Conditional Access Administrator
- Ensure all privileged roles require just‑in‑time elevation
This is Microsoft’s own guidance.
5. Consider secure admin workstations
Depending on where and how you work, consider:
- Providing a dedicated, compliant admin workstation (or fixed IPs for access)
- Enforce all and any admin access through Risked Conditional Access with MFA
- Block admin access from any unmanaged devices
This protects both the organisation and the partner.
Conclusion
This Stryker incident is the latest attack that reminds us that attackers don;’t just use ransomware attacked. Identity is the primary permiter for most and it needs to be protected. Most hackers don’t hack-in, they log in.
If an attacker can compromise the identity and management layer – whether that’s Intune, Meraki, Salesforce, Azure, Microsoft 365, or your CRM – they can revoke access, shut down services, disable trust, break your network and wipe your devices with a click.
The right response is universal Zero Trust:
- Restrict all admin access
- Reduce standing privilege
- Protect every cloud management plane
- Monitor every change
- Treat device and identity trust as dynamic
- Rehearse for partial control‑plane failure
The control plane is now critical infrastructure. Every organisation needs to treat it that way.

Leave a Reply