All Blog Posts
Select a Category or use the search box below.
- Adoption and Change Management (34)
- Agents (8)
- Anthropic (6)
- Anthropic (6)
- Apple (1)
- Asus (1)
- Automation (10)
- AWS (1)
- Business (132)
- Cisco (33)
- Cisco Webex (2)
- Cloud and Data Center (55)
- CloudPC (9)
- Collaboration and Productivity (298)
- Copilot (104)
- Copilot+ PC (16)
- Creativity (13)
- Customer Experience (19)
- Data and AI (96)
- Data Protection (6)
- Dell (1)
- Devices (33)
- Education (5)
- End User Compute (82)
- Enterprise Infrastructure (19)
- Finance (1)
- Geeky Stuff (16)
- Google (1)
- Google (4)
- HPE (1)
- Intel (2)
- Juniper (1)
- Low Code (2)
- Microsoft (207)
- Microsoft Surface (16)
- Microsoft Teams (6)
- Nvidia (1)
- Observability (2)
- OpenAI (13)
- OpenAI (11)
- Palo Alto (1)
- Qualcomm (4)
- Quantum Computing (1)
- Regulatory Compliance (3)
- Security and Compliance (95)
- SharePoint (1)
- Spunk (4)
- Uncategorised (2)
- Vendor (1)
- Windows 10 (49)
- Windows 11 (99)
- WindowsInsider (24)
-
What we can learn from the Stryker Cyber Incident
Read more: What we can learn from the Stryker Cyber IncidentThe recent cybersecurity incident disclosed by Stryker on March 11, 2026, which caused global disruption to an aspect of their Microsoft environment. In their disclosure, Striker said it activated their…
-
With Security Copilot now part of Microsoft 365 E5 – what do you actually get?
Read more: With Security Copilot now part of Microsoft 365 E5 – what do you actually get?At Ignite this week, Microsoft announced that Security Copilot will now be included in Microsoft 365 E5 (and E5 Security) at no additional cost. Security Copilot delivers “AI-powered, integrated, cost-effective,…
-
SMBs – upgrade to Microsoft 365 E5 Security for $12
Read more: SMBs – upgrade to Microsoft 365 E5 Security for $12Microsoft quietly announced yesterday that Microsoft 365 Business Premium customers (this is a SMB license for customers with less than 300 seats) can now add the Microsoft 365 E5 Security…
-
Cisco Live: Every business in the world will become a tech company
Read more: Cisco Live: Every business in the world will become a tech company…and that’s what the innovations and announcements at Cisco Live this week were all centered around. in networking, security, data centers, and more that we unveiled at Cisco Live EMEA…
-
Streamlining Copilot Adoption: Reducing Data Oversharing in Microsoft 365
Read more: Streamlining Copilot Adoption: Reducing Data Oversharing in Microsoft 365One of the concerns I often talk to organisations about, is the fear that Copilot might surface sensitive information that it should not have access to due to IT/Compliance teams…
-
Windows and Devices – Summary of Ignite Announcements
Read more: Windows and Devices – Summary of Ignite AnnouncementsIntroduction Copilot was very much front and center at Microsoft Ignite last month. However, the Windows ecosystem also had lots of coverage. This includes Windows 11, new devices, Windows 365,…
-
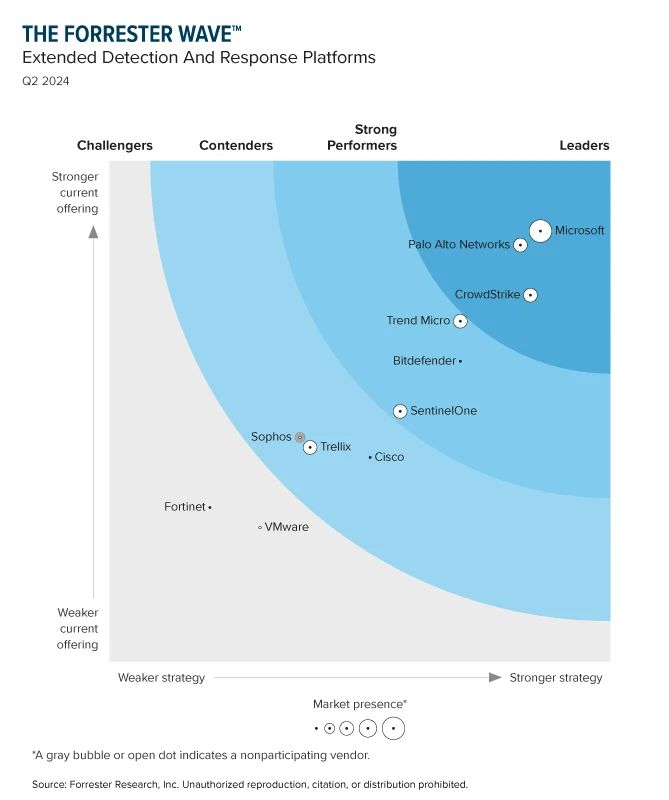
Forrester: Microsoft Leading the Charge in XDR Innovation
Read more: Forrester: Microsoft Leading the Charge in XDR InnovationThis blog post captures Microsoft’s latest achievements, innovations and recognition in cybersecurity as reported by Forrester in their recent wave report on Extended Dedection and Response (XDR) plafforms. Here is…
-
Microsoft’s Copilot for Security available April 1st
Read more: Microsoft’s Copilot for Security available April 1stNo – it’s not an April Fools Joke – Microsoft yesterday (13th March 2024) announced that their much anticpiated Copilot for Security will be available to buy and use from…
-
My 8 AI tech predictions for 2024
Read more: My 8 AI tech predictions for 2024My 8 AI focussed tech predictions for 2024 in include the improvement and competition of generative AI models, the need for more AI and data training, legal and ethical challenges…
-
Microsoft 365 E5 to get Defender for IoT for free
Read more: Microsoft 365 E5 to get Defender for IoT for freeMicrosoft have announced that organisations with Microsoft 365 E5 subscriptions will soon be getting a new “service plan” called “Defender for IoT – Enterprise IoT Security – Enterprise IoT Security”.…
-
Cisco Live 2023 – Cisco’s Key Announcements
Read more: Cisco Live 2023 – Cisco’s Key AnnouncementsYesterday (6th June 2023) was the first day of Cisco Live which was hosted in Las Vegas. CEO Chuck Robbins hosted the keynote, along with a host of product leads…
-
Microsoft 365 Security vs Point Solutions
Read more: Microsoft 365 Security vs Point SolutionsTL;DR Microsoft now claims that they handle, process and act upon more than forty-three trillion daily threat signals. This blog, however, does not go into the specific features and security…
-
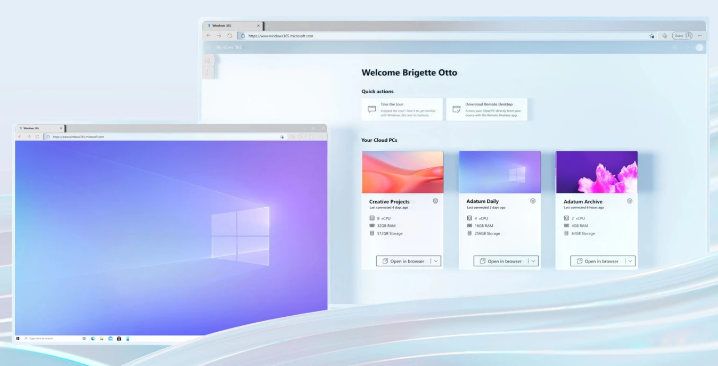
Should every organisation be considering Windows 365?
Read more: Should every organisation be considering Windows 365?Windows 365 has just celebrated its first birthday – but what is it and why is Microsoft betting big on Windows 365 to help improve the employee experience, tighten security,…
-
Microsoft adds “Defender” to more of their Security Products Names
Read more: Microsoft adds “Defender” to more of their Security Products NamesMicrosoft Defends name changes as more Security Products get the “Defender” name tag
-
Windows 11 is now available globally
Read more: Windows 11 is now available globallyHere’s what #Windows11 brings to the table for Business and Consumer for productivity and security in todays hybrid world…..
-
Microsoft now lets you make your password more secure….by removing it completely!
Read more: Microsoft now lets you make your password more secure….by removing it completely!Microsoft has made a giant leap forward in making your online world more secure by making passwords optional for personal MSA accounts like your personal Office 365 account/Hotmail etc. It’s…
-
“Defender for Endpoints” will now be included for free as part of Microsoft 365 E3/A3
Read more: “Defender for Endpoints” will now be included for free as part of Microsoft 365 E3/A3Microsoft have announced a more cost effective endpoint protection plan for Microsoft 365 and Windows customers. Named Microsoft Defender for Endpoint P1 this provides comprehensive threat prevention and protection for…
-
Windows Server and SQL 2008 and 2012 – Extended Support Options
Read more: Windows Server and SQL 2008 and 2012 – Extended Support OptionsSQL and Windows Server 2008 Extended Security Updates were made available (at a cost) by Microsoft for both SQL Server and Windows Server versions 2008 and 2008 R2 since “official…
-
Microsoft announces $10b in Security Revenue and is leading the battle on the Cyber Security Crisis
Read more: Microsoft announces $10b in Security Revenue and is leading the battle on the Cyber Security CrisisI first blogged about the sheer size and capability of Microsoft as a cybersecurity giant about a year ago, but last week Microsoft homed in on this as they highlighted…
-
Microsoft Edge now alerts you if any of your online passwords are leaked!
Read more: Microsoft Edge now alerts you if any of your online passwords are leaked!Let’s face it – all of us re-use our passwords across different systems, and most use one password for pretty much everything they online – and whilst these may be…
-
Microsoft Defender now unifies SIEM and XDR
Read more: Microsoft Defender now unifies SIEM and XDRWhilst some vendors deliver XDR, and some deliver SIEM, the new Microsoft Defender ensures organisations can benefit from using deeply integrated SIEM and XDR for end-to-end visibility and prioritised actionable…
-
“Application Guard” for Office Desktop Apps enters public preview
Read more: “Application Guard” for Office Desktop Apps enters public previewMicrosoft has released a new security feature for Microsoft 365 into Public Preview. This new feature, known as “application guard“, has been designed to help prevent risky, malicious, or untrusted…