All Blog Posts
Select a Category or use the search box below.
- Adoption and Change Management (35)
- Agents (8)
- Anthropic (7)
- Anthropic (6)
- Apple (1)
- Asus (1)
- Automation (10)
- AWS (1)
- Business (132)
- Cisco (33)
- Cisco Webex (2)
- Cloud and Data Center (55)
- CloudPC (9)
- Collaboration and Productivity (299)
- Copilot (107)
- Copilot+ PC (18)
- Creativity (13)
- Customer Experience (19)
- Data and AI (97)
- Data Protection (6)
- Dell (1)
- Devices (33)
- Education (5)
- End User Compute (83)
- Enterprise Infrastructure (19)
- Finance (1)
- Geeky Stuff (16)
- Google (1)
- Google (4)
- HPE (1)
- Intel (2)
- Juniper (1)
- Low Code (2)
- Microsoft (208)
- Microsoft Surface (18)
- Microsoft Teams (6)
- Nvidia (2)
- Observability (2)
- OpenAI (11)
- OpenAI (13)
- Palo Alto (1)
- Qualcomm (4)
- Quantum Computing (1)
- Regulatory Compliance (3)
- Security and Compliance (95)
- SharePoint (1)
- Spunk (4)
- Uncategorised (2)
- Vendor (1)
- Windows 10 (49)
- Windows 11 (99)
- WindowsInsider (24)
-
Cisco announces “AI Assistant for Security”
Read more: Cisco announces “AI Assistant for Security”Last month, and now just a few weeks away from Cisco Live, Cisco have announced they are bringing a new “AI Assistant for Security” to market this year. This is…
-
Cisco acquires Armorblox, bolstering their Security offerings
Read more: Cisco acquires Armorblox, bolstering their Security offeringsCisco have announced that they are to acquire Armorblox, a leading email security house whose portfolio (which is centred around email protection) includes email security, DLP, data encryption, impersonation protection,…
-
Microsoft Defender named “Leader” in the latest Gartner Magic Quadrant for Endpoint Protection Platforms
Read more: Microsoft Defender named “Leader” in the latest Gartner Magic Quadrant for Endpoint Protection PlatformsAnother Gartner Quadrant another winning result – as yet again, Microsoft continues it’s move up the quadrant – this year storming ahead of their competition in the Endpoint protection category…
-
Microsoft Sentinel |2022 Gartner Magic Quadrant leader | Security Information & Event Management
Read more: Microsoft Sentinel |2022 Gartner Magic Quadrant leader | Security Information & Event ManagementMicrosoft has been named a Leader in the 2022 Gartner Magic Quadrant for Security Information and Event Management (SEIM) and was positioned highest on the measure of Ability to Execute…
-
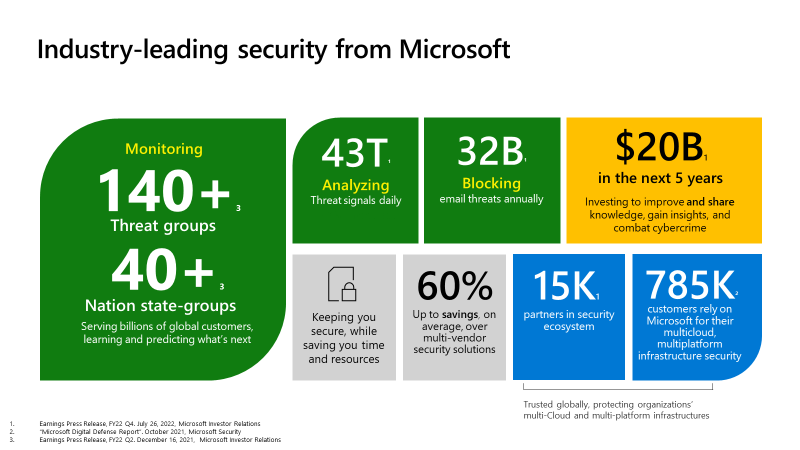
Microsoft 365 Security vs Point Solutions
Read more: Microsoft 365 Security vs Point SolutionsTL;DR Microsoft now claims that they handle, process and act upon more than forty-three trillion daily threat signals. This blog, however, does not go into the specific features and security…
-
Defending Ukraine: Microsoft share conclusions of their cyber-attacks’ defensives against Russian attacks
Read more: Defending Ukraine: Microsoft share conclusions of their cyber-attacks’ defensives against Russian attacksAs Russia continues its attack on Ukraine, Microsoft has taken some of the lessons they have learnt from their cyber attack defensive assistance of Ukraine at the start of the…
-
Microsoft to acquire cyber intelligence research expert Miburo
Read more: Microsoft to acquire cyber intelligence research expert MiburoMicrosoft continues its huge investment and expansion of their leading cyber security, threat analysis and response solutions with the acquisition of Milburo, a world leader in foreign threat analysis and…
-
Windows Autopatch is now available for public preview
Read more: Windows Autopatch is now available for public previewWindows Autopatch, a service to automatically keep Windows and Microsoft 365 up to date in enterprise organisations, has now reached public preview. When officially released (GA), it will be included…
-
Microsoft announces new Managed ‘Security Experts Services’ to ramp up fight against cybercrime
Read more: Microsoft announces new Managed ‘Security Experts Services’ to ramp up fight against cybercrimeMicrosoft’s security business is growing faster than any of their other mainstream products and services, and today they announced they will be adding three new services designed to help organisations…
-
Smaller Organisations – Here’s why you should care about Microsoft Defender for Business
Read more: Smaller Organisations – Here’s why you should care about Microsoft Defender for BusinessToday (May 3rd 2022) Microsoft formally announced the general availability of the standalone version of Microsoft Defender for Business. Why should I care? Well firstly, it’s a myth that smaller…
-
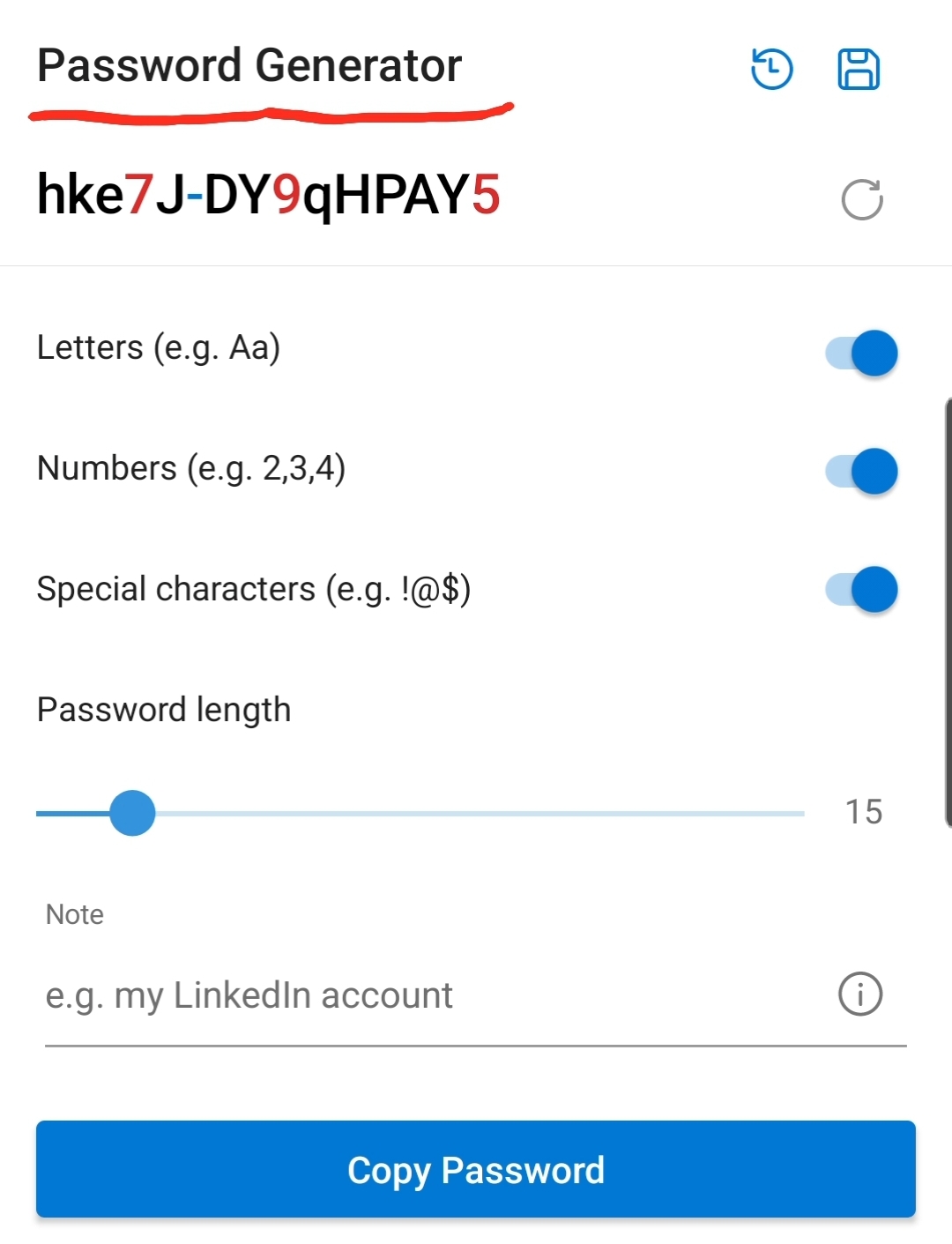
Microsoft Authenticator adds ability to generate Secure Passwords for you.
Read more: Microsoft Authenticator adds ability to generate Secure Passwords for you.To mark the one year anniversary since Microsoft launched their Autofill feature on Authenticator, they have just updated the service with the ability to auto generate strong, unique passwords for…
-
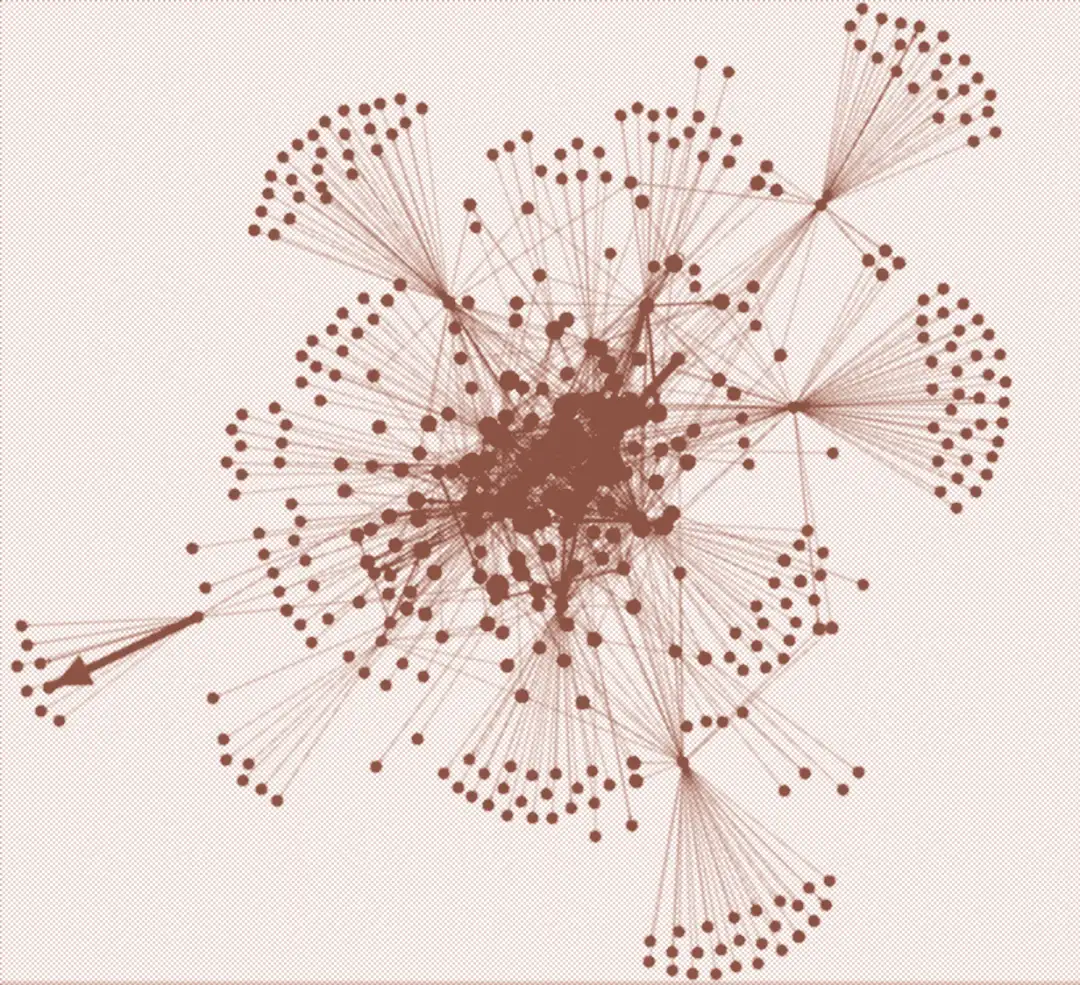
Microsoft’s new “Cyber Signals” gives vital insights into current cybersecurity threats
Read more: Microsoft’s new “Cyber Signals” gives vital insights into current cybersecurity threatsMicrosoft has launched their first Cyber Signals, a new quarterly cyber intelligence brief that highlights the latest cyber security threats, tactics, and strategies and is aimed at Chief Information Security…
-
Microsoft adds “Defender” to more of their Security Products Names
Read more: Microsoft adds “Defender” to more of their Security Products NamesMicrosoft Defends name changes as more Security Products get the “Defender” name tag
-
Microsoft and Rubrik Partner to bolster Zero Trust,and Ransomware protection
Read more: Microsoft and Rubrik Partner to bolster Zero Trust,and Ransomware protectionMICROSOFT and Rubrik (a US-based, Gartner leading data backup and protection company) have announced a new strategic partnership which will see them working together to providing Zero Trust data protection…
-
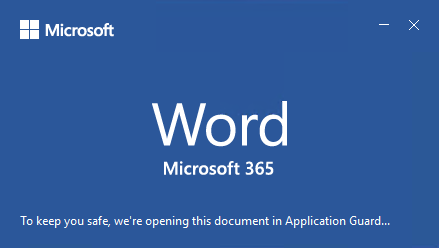
“Application Guard” for Office Desktop Apps enters public preview
Read more: “Application Guard” for Office Desktop Apps enters public previewMicrosoft has released a new security feature for Microsoft 365 into Public Preview. This new feature, known as “application guard“, has been designed to help prevent risky, malicious, or untrusted…
-
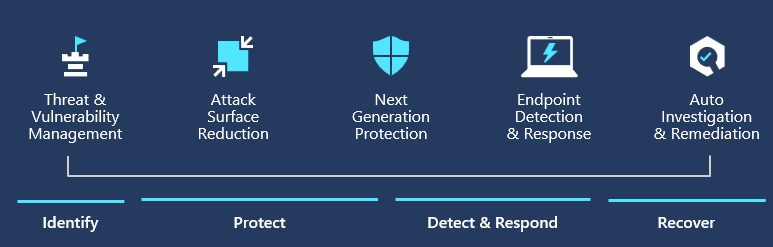
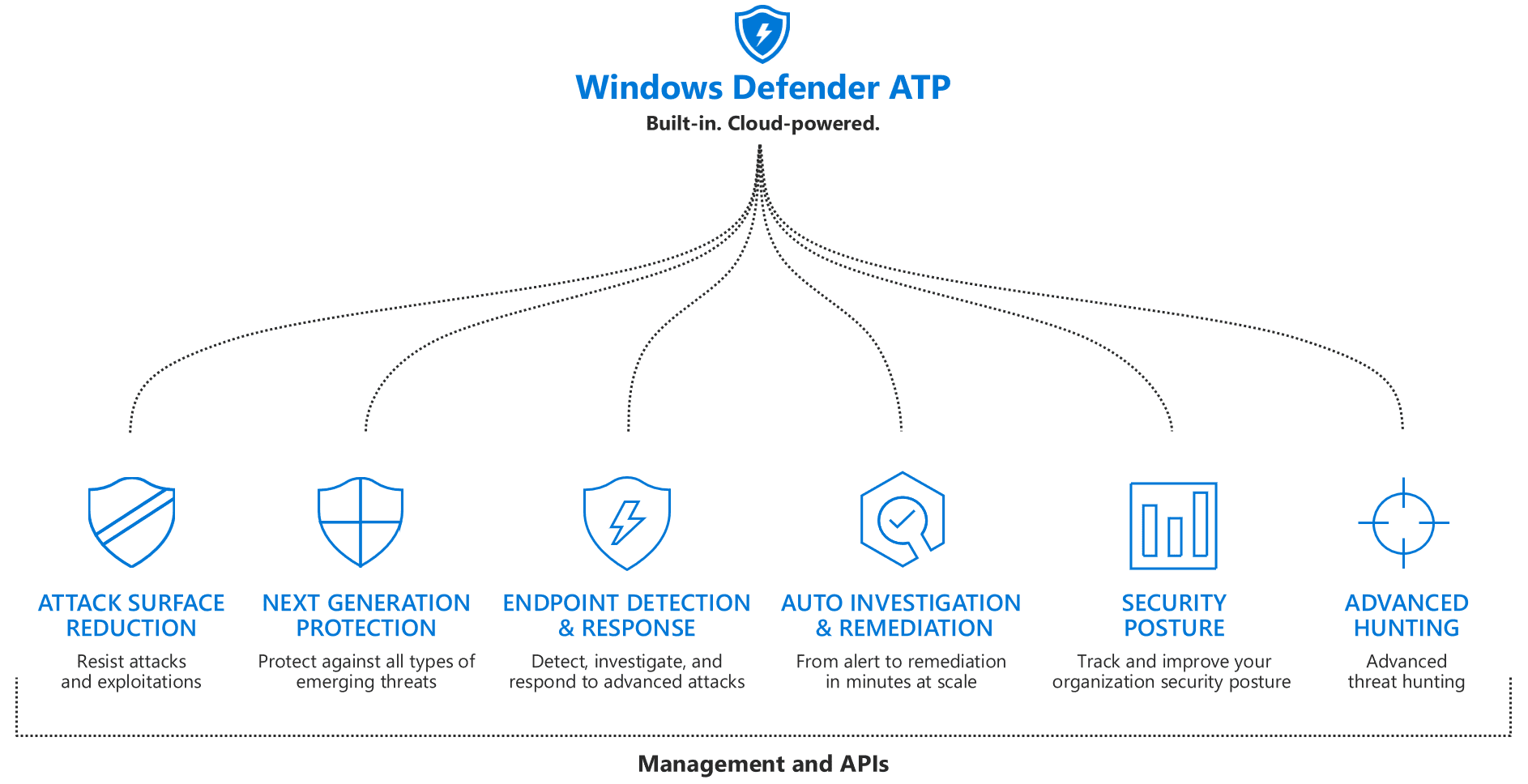
Revamped alert page now live in Microsoft Defender ATP
Read more: Revamped alert page now live in Microsoft Defender ATPRevamped alert page now live in Microsoft Defender ATP @msdefenderatp @microsoft365