Windows Autopatch, a service to automatically keep Windows and Microsoft 365 up to date in enterprise organisations, has now reached public preview. When officially released (GA), it will be included Microsoft commercial customers with a Windows Enterprise E3 license or higher.
In short, Windows Autopatch automatically allows organisation to shift the management and deployment of Windows 10, Windows 11 and Microsoft 365 Apps including quality and feature updates, drivers, firmware to Microsoft.
What’s the purpose?
Essentially this aims to take the nightmare out of the age-old “patch Tuesday” and promises to be a great time saver for IT admins. With Autopatch, IT can continue to use their existing tools and processes for managing and deploying updates to devices OR can look to phase in or replace this in entirety and with this new “hands off” approach and let Windows Autopatch take care of security, driver and firmware updates.
“Changing the way things get done, even when that change makes things easier, gives pause to most people who run large IT organisations. By joining the public preview, you’ll be able to get comfortable with Windows Autopatch and ready your organisation to take advantage of the service at scale”.
Lior Bela | Senior Product Marketing Manager | Microsoft
The main purpose of Windows Autopatch is moving the update orchestration burden from the IT department to Microsoft. Once deployed, configured and tested, Autopatch should allow the entire effort around planning and managing the Windows Update process (sequencing and rollout) to be taken away from IT freeing up time and resources.
“Whenever issues arise with any Autopatch update, the remediation gets incorporated and applied to future deployments, affording a level of proactive service that no IT admin team could easily replicate,” Bela added.
“Whenever issues arise with any Autopatch update, the remediation gets incorporated and applied to future deployments, affording a level of proactive service that no IT admin team could easily replicate.”
Lior Bela | Senior Product Marketing Manager | Microsoft
How to enable Autopatch
Windows Autopatch devices must be managed by Microsoft Intune for this to work and Intune must be set as the Mobile Device Management (MDM) authority or co-management must be turned on and enabled on the target devices.
As you’d expect, there are a handful of steps needed to enable the preview and to enrol your Microsoft 365 tenant into the Windows Autopatch public preview:
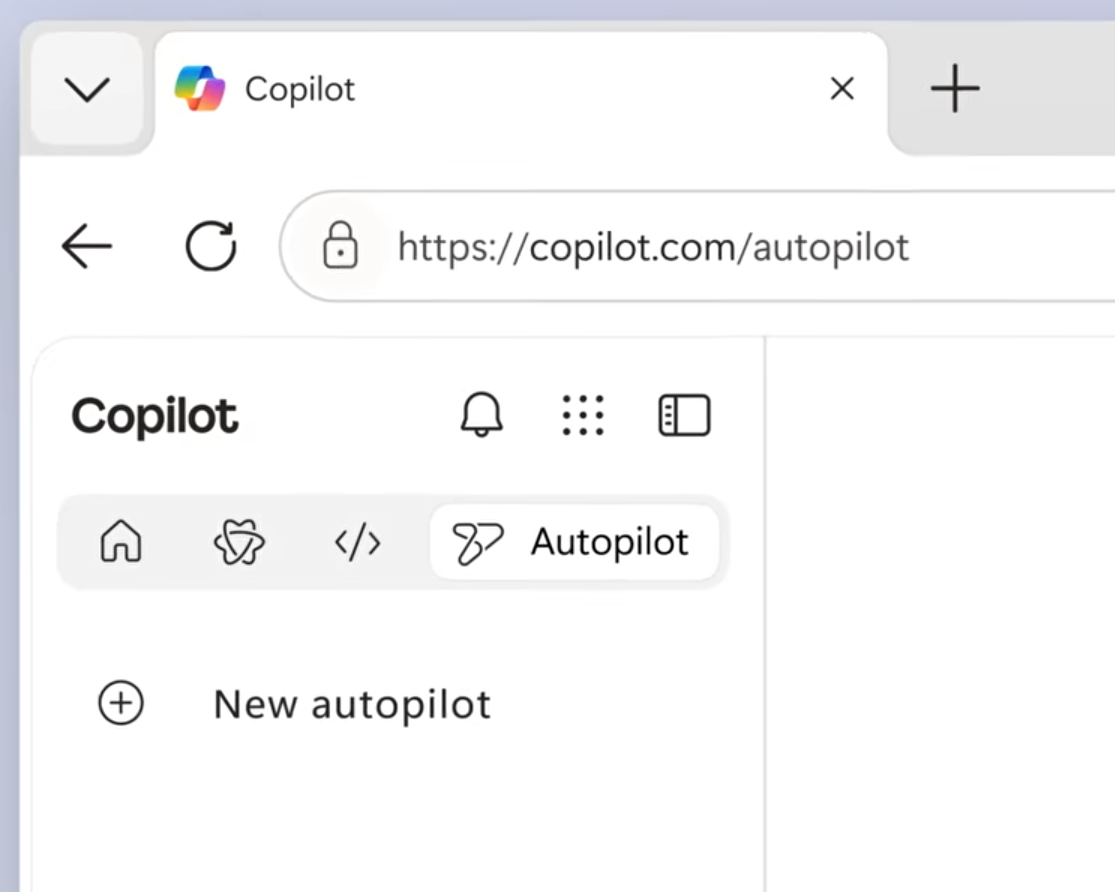
- Log on to Endpoint Manager as a Global Admin and navigate to the Windows Autopatch blade which is under the Tenant Administration menu – this will only be visible if you have the right licenses deployed.
- Using an InPrivate browser window, redeem your Autopatch preview code
- Run the readiness assessment, add the required admin contact, and add the devices you want to enrol in the service.
- Tick the box, to allow Microsoft to manage updates on behalf of your organisation.

Microsoft provides regularly updated instructions on how to add devices to your test ring and how to resolve common errors such as “tenant not ready,” “device not ready” or “device not registered.”
Microsoft also provides detailed instructions (and video) on how to add devices to your test ring and how to resolve the status of “tenant not ready,” or a status of “device not ready” or “device not registered.”
How Autopatch works
The Windows Autopatch service automatically splits your organisation’s device estate into four groups of devices described by Microsoft as “testing rings”.
- Test Ring: Contains a minimum number of devices for test purposes
- First Ring: Contains ~1% of all endpoints (think of this like the early adopter ring)
- Fast Ring: Contains ~9% of devices
- Broad Ring: Contains the rest of the devices.
The updates are deployed progressively, starting with the test ring and moving to the larger sets of devices following a validation period in which the system and IT can monitor device performance and compare it to pre-update metrics through End Point Analytics.

Autopatch also features a nifty, feature called “Halt and Rollback” that block updates from being applied to higher test rings or rolled back automatically. This is key for critical dates or projects which may be impacted by updates or where quality errors are detected in the Test Ring updates.
What about Patch Tuesday and Critical Updates?
Microsoft will continue to deliver monthly security and quality updates for supported versions of the Windows on the second Tuesday of the month (commonly referred to Patch Tuesday or Update Tuesday) as they have been to date. These will be delivered by Autopatch also.
For normal updates, Autopatch uses a regular release cadence starting with devices in the test ring and completing with general rollout to broad ring.
Any updates addressing a critical vulnerability, such as Zero Day threats, will be expedited by Windows Autopatch with a aim to patch all devices immediately.
Microsoft provides further info in the Windows Autopatch support documentation, including details on service eligibility, prerequisites, licensing and features.



Leave a Reply